Decoding Digital Stalking
Understanding how stalkers use technology — and how to detect and document it.
The Evidence Trail
How VigilWatch helps you capture and export the proof you need.
Documented incidents of BLE tracker stalking and WiFi-based attacks — and exactly how VigilWatch detects, alerts, and helps document each threat type for law enforcement.
Cases are based on publicly reported incidents from 2024–2025. Names and case details sourced from court records and law enforcement reports. VigilWatch detection sections are illustrative based on app capabilities.
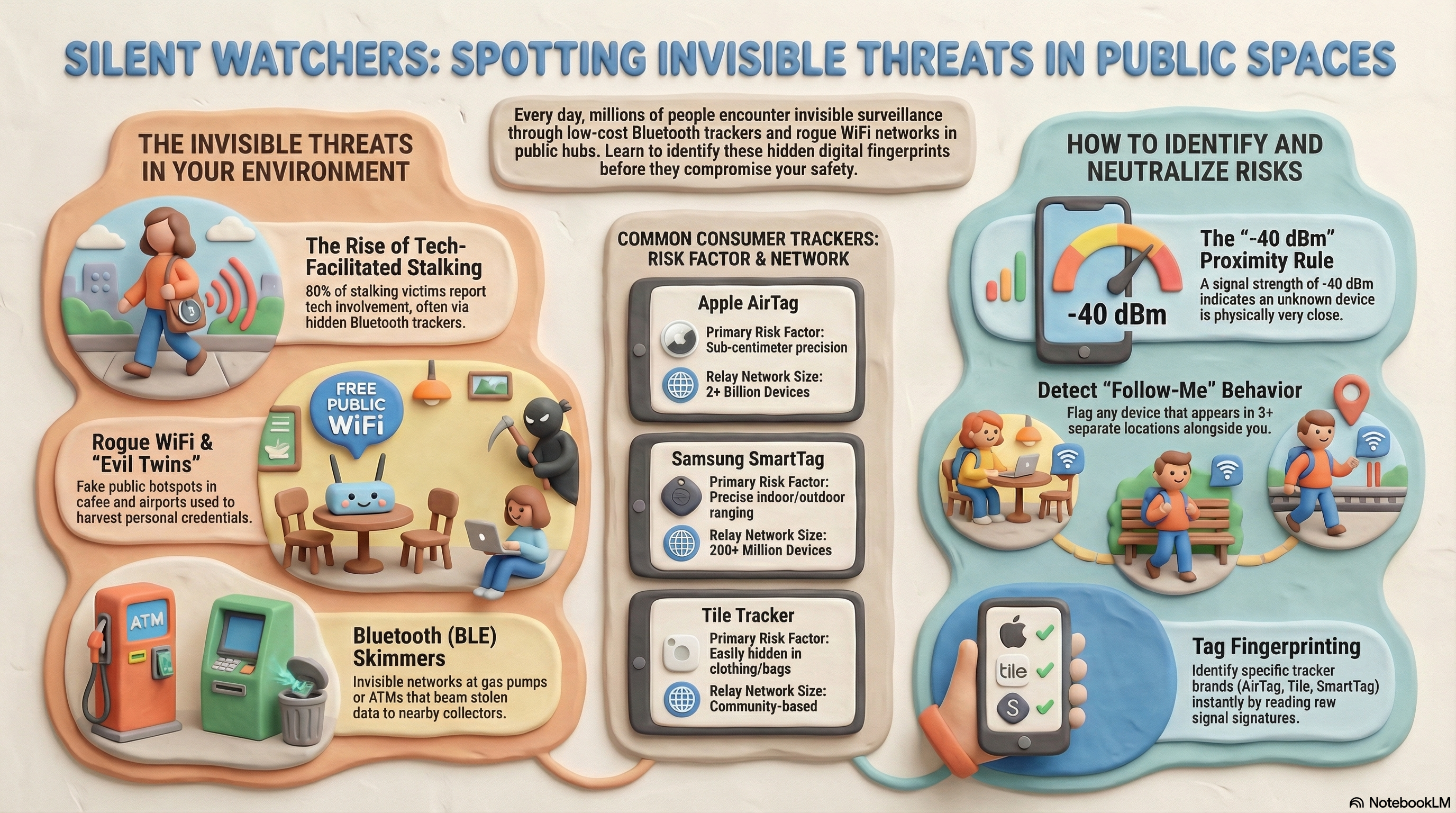
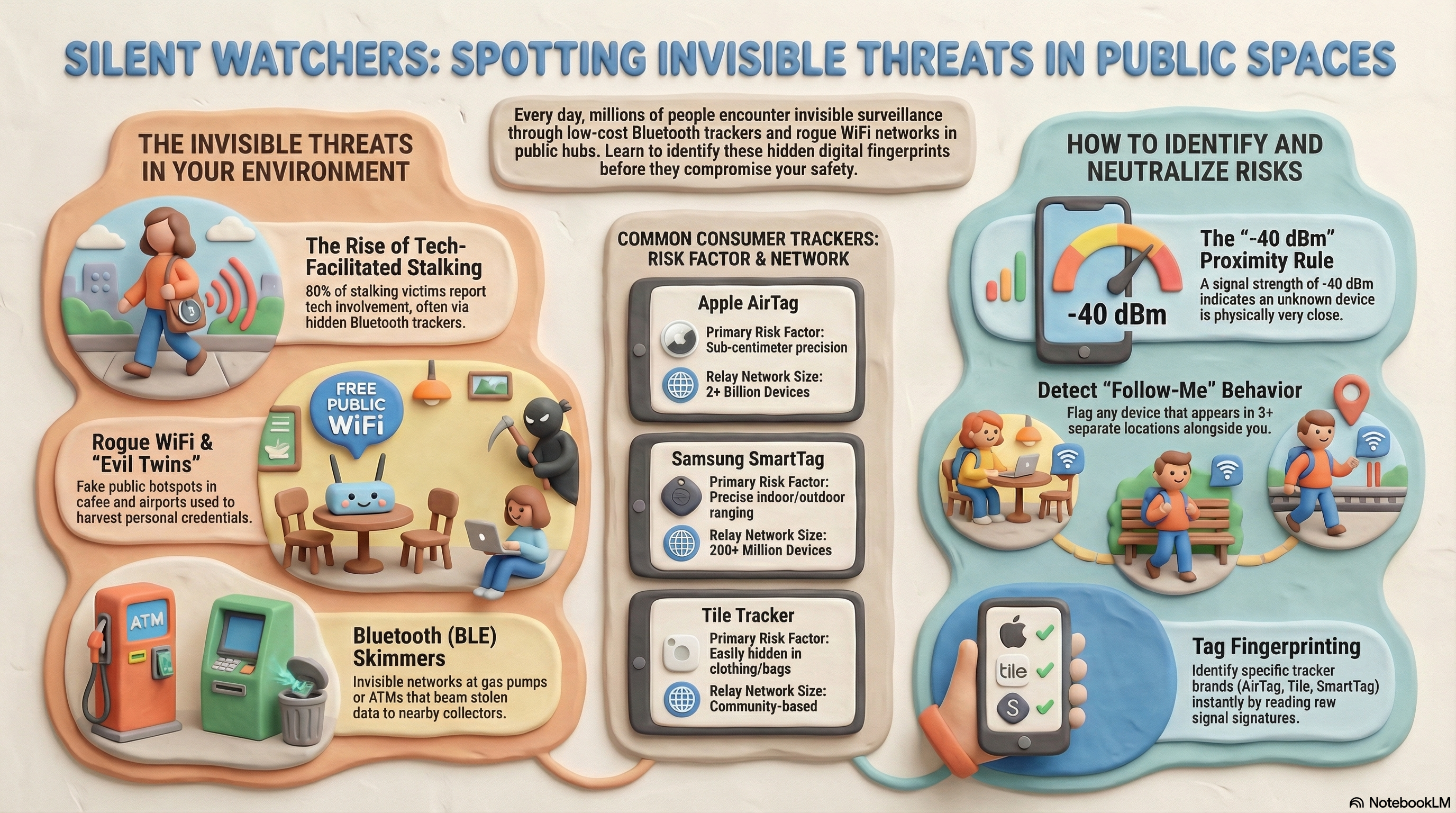
AirTags, SmartTags, and Tile trackers have been weaponized in stalking and domestic abuse — hidden in wheel wells, bumpers, bags, and children's belongings. These are documented incidents from 2024–2025.
Fort Myers police discovered an Apple AirTag hidden inside a vehicle belonging to Nicholas Brezina's ex-wife during an active investigation in mid-February 2026. Brezina was arrested and charged with installing a tracking device without consent — a violation of Florida law.
The case highlights how BLE trackers designed for locating lost items — and distributed through Apple's vast Find My network — are routinely repurposed as silent, long-range surveillance tools against intimate partners. The device required no phone pairing with the victim, no line of sight, and no technical skill to deploy.
James Kleeman, a part-time prisoner transport deputy with the Volusia County Sheriff's Office, allegedly placed multiple Apple AirTags in both his ex-girlfriend's vehicle and her adult daughter's vehicle after their February breakup. The victim first received AirTag alerts and discovered devices as far back as 2025, with additional placements confirmed after the relationship ended.
Ring camera footage captured Kleeman crawling under one of the vehicles with a flashlight during a covert device placement. He admitted to placing the AirTags but denied following the victims. On the day of his arrest, his marked sheriff's vehicle was reportedly spotted near the victim's location while she was giving a statement to detectives in DeLand.
A woman entered her car and immediately received an AirTag connection alert on her phone. Police located a device duct-taped to the rear passenger-side wheel well. Her ex-boyfriend, Danish Ali, admitted placing it after their breakup to track her movements.
The AirTag's serial number and the last four digits of Ali's phone number directly linked the device to him — providing law enforcement with unambiguous evidence.
Suspects taped an AirTag under a couple's vehicle bumper in a public parking lot. They then followed the couple home and robbed them at their residence. Security video captured the robbery. Police recovered the AirTag and confirmed it was used to track the victims' exact route and home address.
This pattern — using BLE trackers not for surveillance but for coordinating home invasions — has been reported in multiple cities. Ex-partners and organized theft rings have used the same tactic for vehicle theft follow-ups.
A woman received repeated phone notifications about an unknown AirTag but didn't understand their significance. Her ex-partner had glued a tracker under her car bumper. Her daughter later received the same alerts, leading to discovery of the device.
This case reflects a devastating UK trend: AirTag and GPS stalking rose 896% (from 57 to 568 cases) by end-2024, mostly linked to coercive control and domestic abuse. BLE trackers were connected to a 1,034% rise in coercive control cases during the same period.
A woman received an AirTag alert after a court hearing with her ex-husband. She found and disabled one device in her car — but alerts persisted for months. Police involvement failed to stop the stalking. She later discovered a second AirTag hidden in her son's pencil bag, allowing her ex-husband to track her movements even after the first device was removed.
The inability to remotely disable trackers, the emotional and professional toll (forcing her to abandon her acting career and relocate), and the failure of Apple's safety features are at the core of an ongoing class-action lawsuit. At least two murders have been linked to AirTag tracking in similar domestic cases.
Understanding how these attacks work helps VigilWatch detect them faster.
Wheel wells, bumpers, children's belongings, purses, gym bags. Strong RSSI in VigilWatch (-40 to -55 dBm) pinpoints physical closeness before visual search.
Starts as "Unknown" device. Becomes persistent. Follow Score rises over days. ESCALATING trend badge appears. Then used to coordinate a crime or continue coercive control.
Anxiety, career loss, forced relocation, and in the worst cases, physical violence. 80% of stalking involves technology; 14%+ uses location tracking devices specifically.
In every conviction above, the device's traceable data was key. VigilWatch's timestamped location timeline + PDF case number provides the same level of documentation — from your phone, instantly.
Evil twin networks, rogue access points, and WiFi-based surveillance — used in airports, cafés, apartments, and domestic abuse situations.
A 44-year-old IT-savvy man carried a portable WiFi Pineapple device onto domestic flights and used it at airports across Perth, Melbourne, and Adelaide. He created "evil twin" networks mimicking legitimate airport and airline WiFi SSIDs — tricking passengers into connecting.
Victims who connected encountered fake login pages designed to capture credentials. The attacker then used those credentials to access social media, email accounts, and intimate photos and videos of multiple women. Australian Federal Police confirmed he also passively listened for device probe requests to gather data without requiring a connection.
Flight crew spotted the suspicious network and alerted authorities. He was arrested in April 2024.
The same perpetrator (and parallel uncharged patterns) deployed fake free WiFi networks — often named "FREE_PUBLIC_WIFI" or mimicking café names — in public spaces. Victims connected assuming the network was legitimate, allowing the attacker to capture login credentials, monitor web activity, and in some cases harvest intimate files.
Beyond active connections, probe requests from phones (where a device automatically asks "is my saved network nearby?") allowed passive tracking of device presence even without the victim fully connecting. This technique requires no interaction from the victim — just physical proximity.
Residents in a shared apartment building reported that a neighbor repeatedly hacked into their WiFi and monitored their devices. The attacker used rogue access points or deauthentication attacks to force device reconnections, then intercepted unencrypted traffic to access private Facebook activity, group chats, and intimate online behavior.
Victims described the attacker demonstrating knowledge of private conversations — only possible through network interception. This hybrid cyber-physical stalking leveraged close physical proximity (same building) combined with WiFi exploitation, making traditional security tools ineffective.
Advanced research and documented real-world cases show that attackers can use commodity WiFi receivers or planted rogue access points to track movement inside homes through signal strength fluctuations — without the victim ever connecting to any network. This technique infers occupancy, room-level activity, and daily routines from the RF environment alone.
In domestic abuse contexts, abusers have exploited shared home networks or planted small WiFi-enabled devices (including modified IoT gadgets) to maintain surveillance of victims after they've severed digital connections. This attack is particularly insidious because the victim never receives any notification — there's nothing to dismiss.
Real-time unknown BLE and WiFi device detection. Toggle BT and WiFi independently. Animated radar visualizes signal proximity the moment a device appears.
3+ distinct locations + Follow Score ≥ 50 triggers detection banner. HIGH confidence at 75+. Haversine formula clusters real-world GPS locations 50m+ apart.
Named zones (Home/Office, 50–500m radius) with device counts. Alerts fire on new Unknowns, "Seen N times," zone entry, or confirmed Follow-Me detection.
Mark as Threat or Concern instantly. View Bluetooth services list, RSSI guide, manufacturer info, times seen. Apple Find My UUID identifies AirTag-class devices.
Per-device emergency toggle: screen strobes red, full-screen modal with device info, heavy haptics. Persists until dismissed. Works independently per device for multi-tracker situations.
PDF report with unique case number (VW-YYYYMMDD-XXXX), full location timeline, Daily Pattern clock, 14-day Frequency Trend, and legal disclaimer — ready for law enforcement in seconds.
Illustrative scenarios showing the environments where VigilWatch matters most.
BLE tracker follows same route every day — COMMUTE pattern detected.
BLE sniffer at -38 dBm — same-room signal — flagged on Continuous scan.
Same BSSID appears across multiple café visits — mobile rogue AP confirmed.
Strong-signal unknown device triggers Alert Immediately in a parking garage.
BLE scanner on platform detected across multiple commutes — WORKDAY OVERLAP.
Tracker placed in lot. VigilWatch detects it before the drive home begins.
Understanding how stalkers use technology — and how to detect and document it.
How VigilWatch helps you capture and export the proof you need.
These are the kinds of situations people post about every day on Reddit — in r/privacy, r/TwoXChromosomes, r/Stalking, r/whatisit, and r/cybersecurity. VigilWatch was built for every one of them.
"Found this taped under my car. Someone's been sending me weird texts knowing things they shouldn't. What is this thing?"
VigilWatch would have flagged the tracker days earlier — detecting the same unknown Bluetooth device appearing at your home, workplace, and every stop in between, long before you noticed the texts.
"What's the best app to detect unknown Bluetooth devices near me? I keep seeing the same device name pop up wherever I go."
The Follow-Me Detection engine scores every persistent device across 5 dimensions — frequency, multi-location overlap, RSSI proximity, time-of-day patterns, and zone entry. One unknown device following you gets caught. Fast.
"Got an 'Unknown AirTag following you' alert. I found it and disabled it — but is there anything else I should be watching for?"
Apple only alerts on its own ecosystem. VigilWatch catches all Bluetooth trackers — Tile, Samsung SmartTag, off-brand devices, and hardware fingerprints — and builds a multi-location timeline you can export as a legal PDF.
"Does anyone know of an app that can tell me if my abuser planted a tracker on me? I'm trying to document everything."
VigilWatch requires no account and uploads nothing. Evidence exports include a unique case number, GPS-stamped timeline, signal frequency charts, and a legal disclaimer — formatted for law enforcement submission.
"How do I detect an evil twin WiFi attack on my phone? I'm on public WiFi a lot for work."
VigilWatch's WiFi scanner monitors for rogue access points — networks with matching SSIDs but mismatched signal behavior — and flags them before your phone connects. Most VPNs don't warn you until after the fact.
"I think someone put a tracker on my car at the mall to follow me home. Is that actually a thing? What can I do?"
It's a documented theft method. Run VigilWatch in Continuous mode after visiting high-traffic areas — parking lots, malls, airports. Any new tracker that stays with you across locations gets flagged within minutes.
These communities exist because the threat is real and growing. In 2025 alone, over 100 criminal charges were filed in the US tied to covert Bluetooth tracking devices — the highest spike since AirTags launched.
Free. No account. No cloud. Every scan is private. The evidence export could make the difference.
If you are in immediate danger, call 911 (US) or your local emergency services first.