
Coming Soon!

Coming Soon!
VigilWatch fingerprints AirTags, Tiles, and Samsung SmartTags by their raw BLE signatures — no Apple ecosystem required. Detects rogue WiFi networks, maps Follow-Me patterns across locations, and generates court-ready evidence. Professional-grade surveillance detection in your pocket.
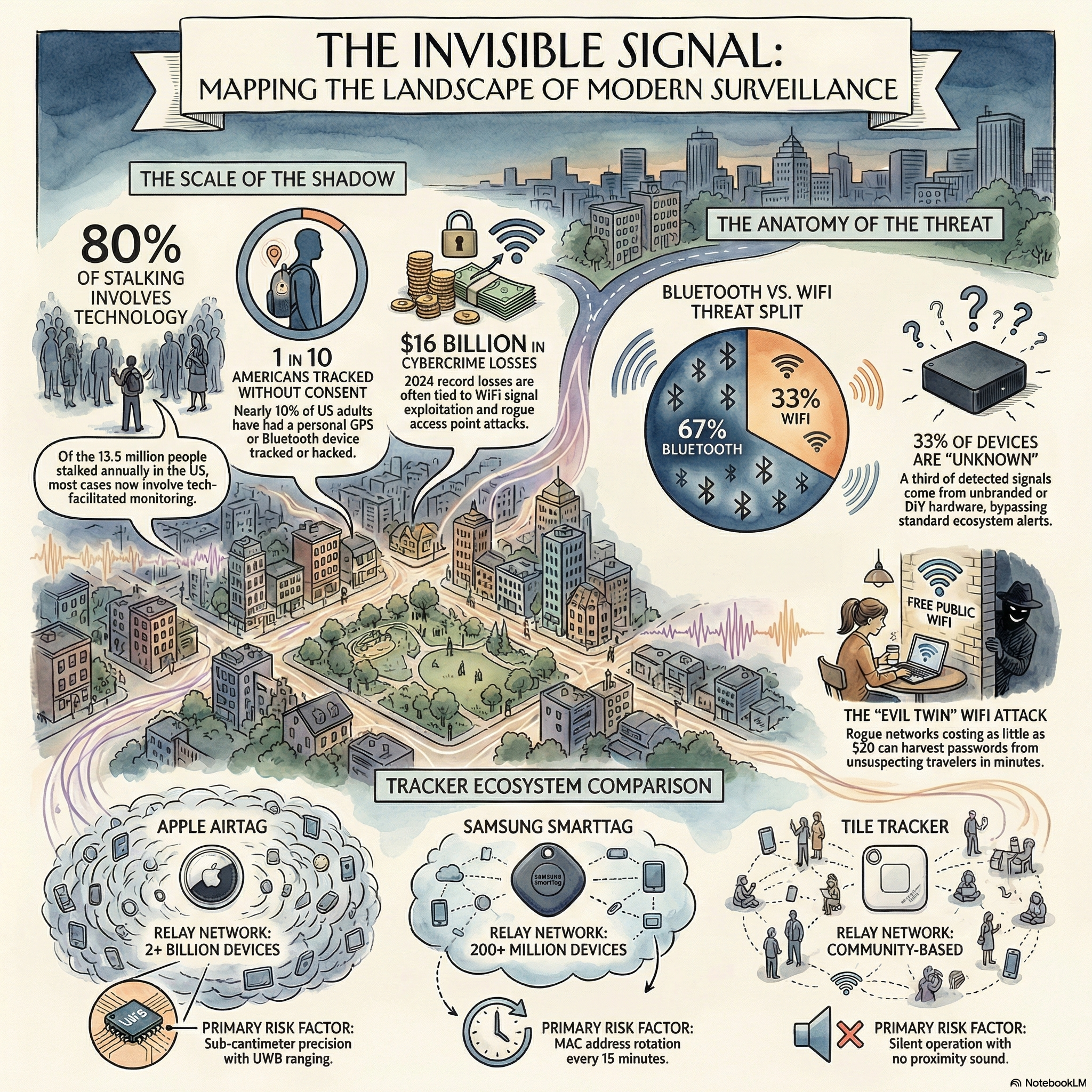
A $29 AirTag. A $25 Tile. A $99 WiFi Pineapple from Amazon. The criminal doesn't need technical skill — just five minutes alone with your car. Meanwhile, the tools to detect these threats have been locked inside Apple's ecosystem, delayed by hours, or simply nonexistent for most people.
VigilWatch closes that gap.
VigilWatch gives you the same RF awareness used by security professionals — in a clear, private app anyone can use. The only app with WiFi + BLE scanning, behavioral analytics, and legal-grade evidence export.
Bypasses vendor notification systems by reading raw BLE advertisements directly. Identifies AirTags (UUID 0x4C00), Tile (0x00CC), Samsung SmartTag (0xFD5A), and 4 more tracker brands — on any device, regardless of ecosystem.
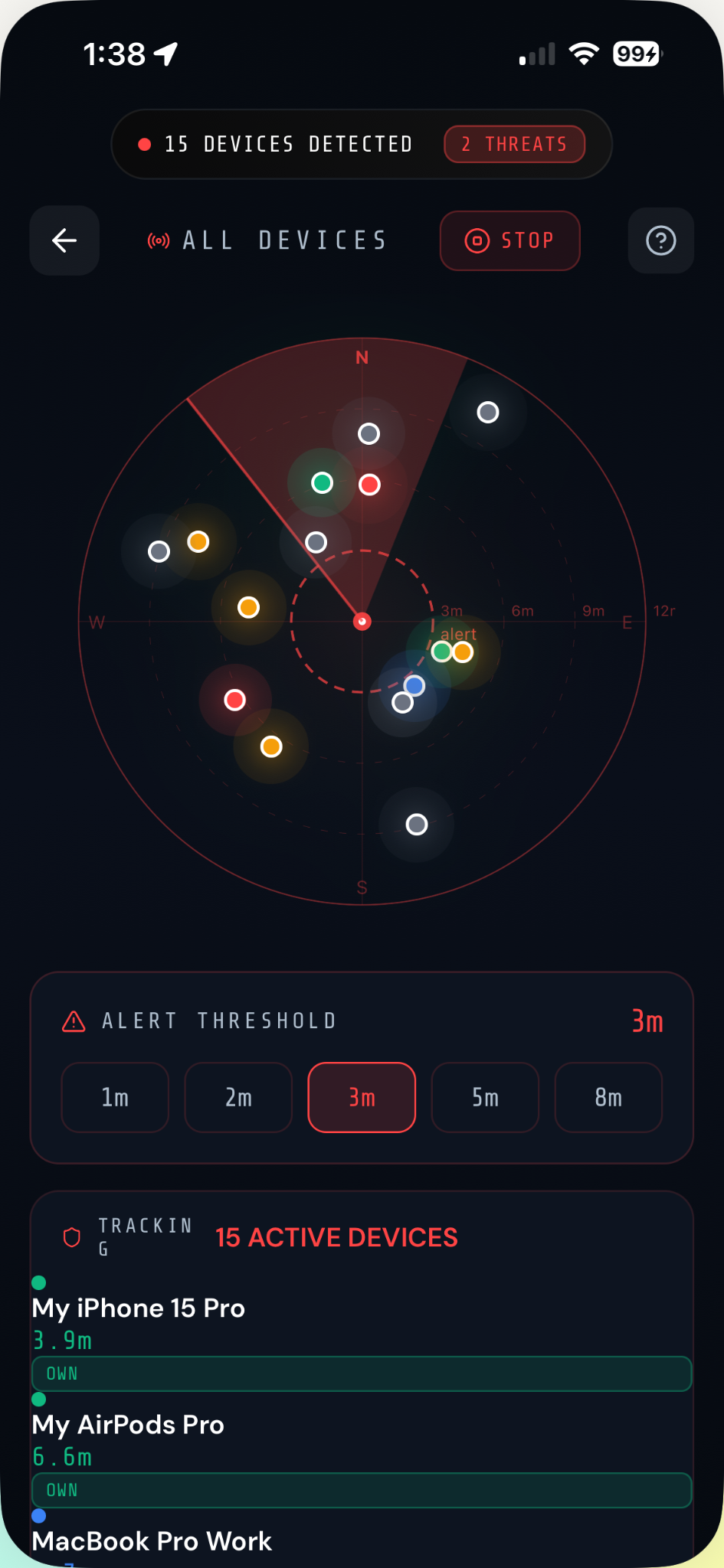
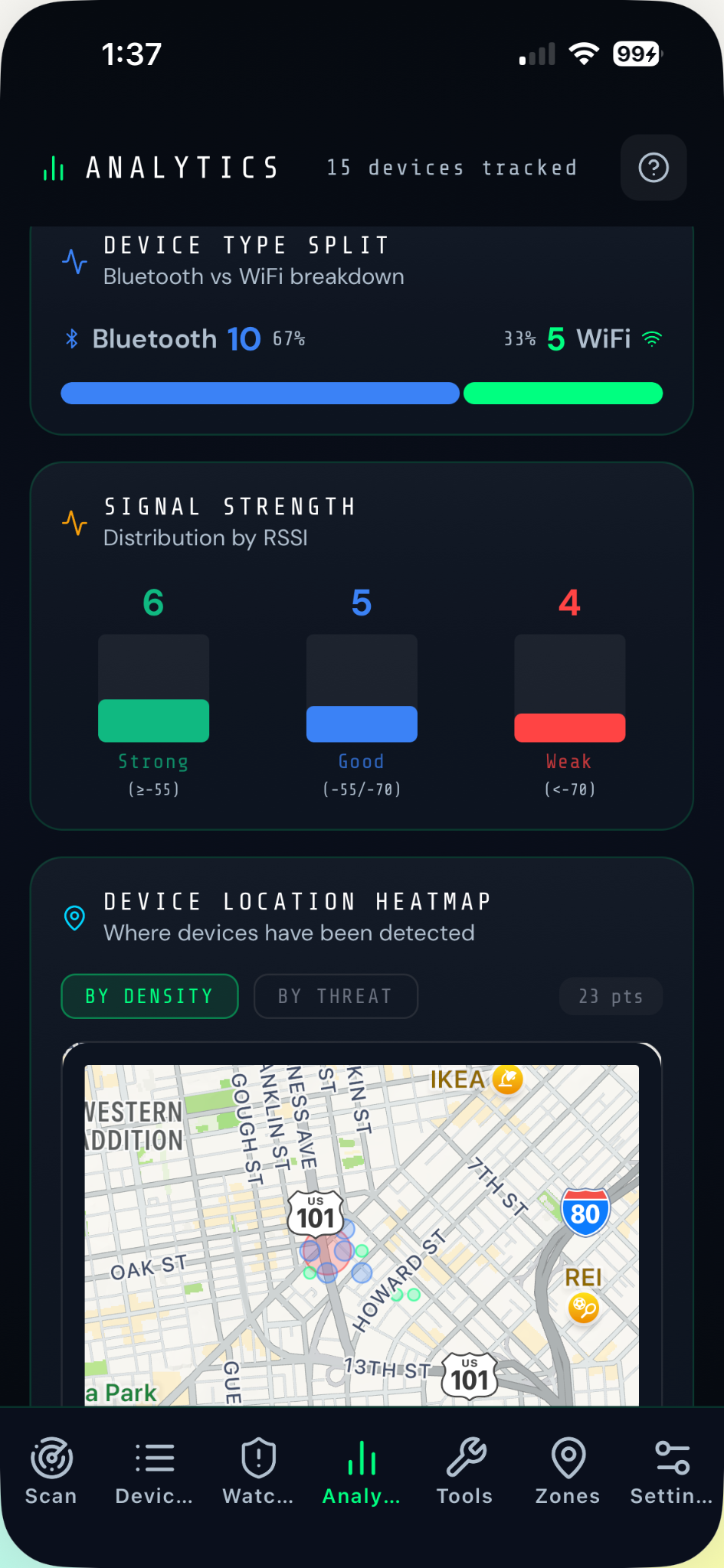
Detects all nearby Bluetooth (BLE + Classic) and WiFi access points. Manual, Continuous, or background Interval modes. Live feed shows RSSI, device type, and threat level in real time.
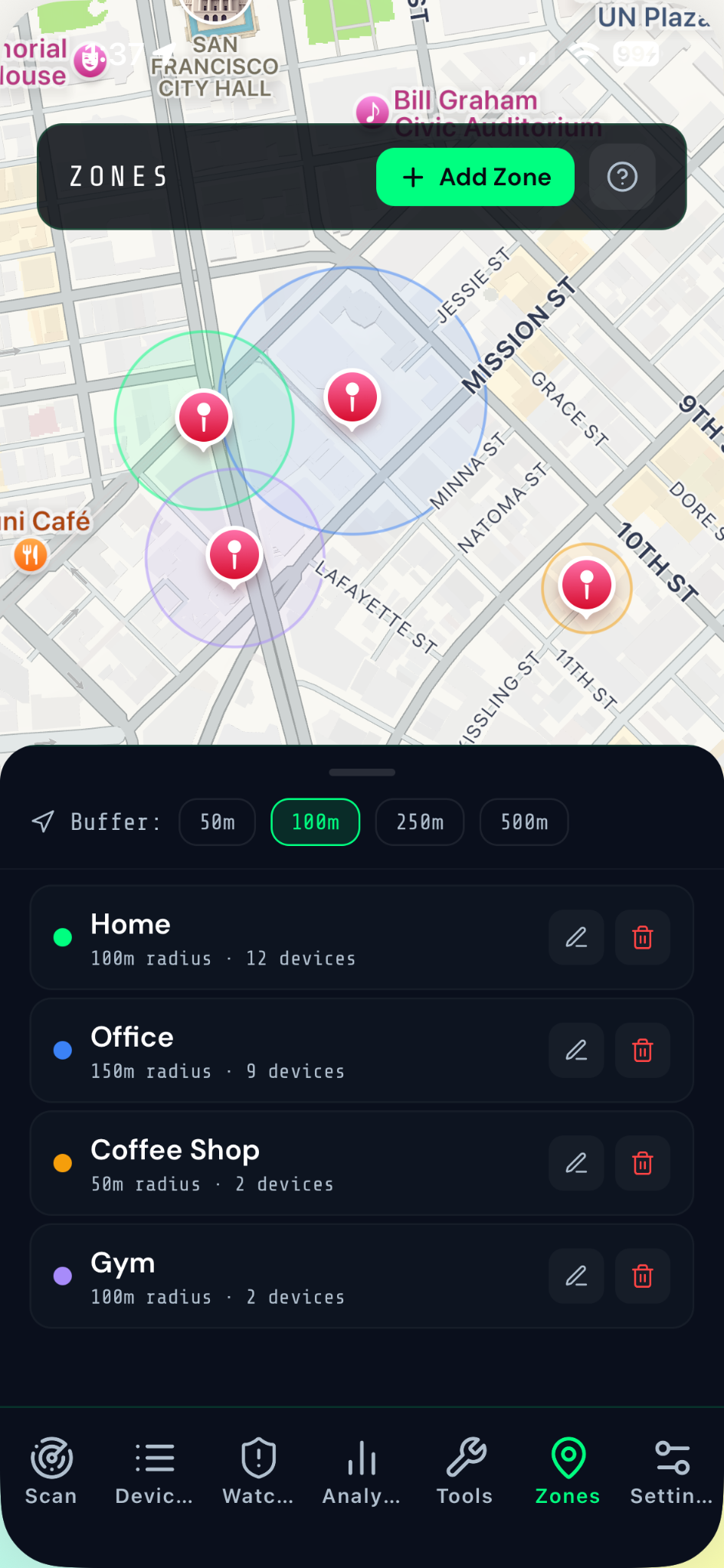
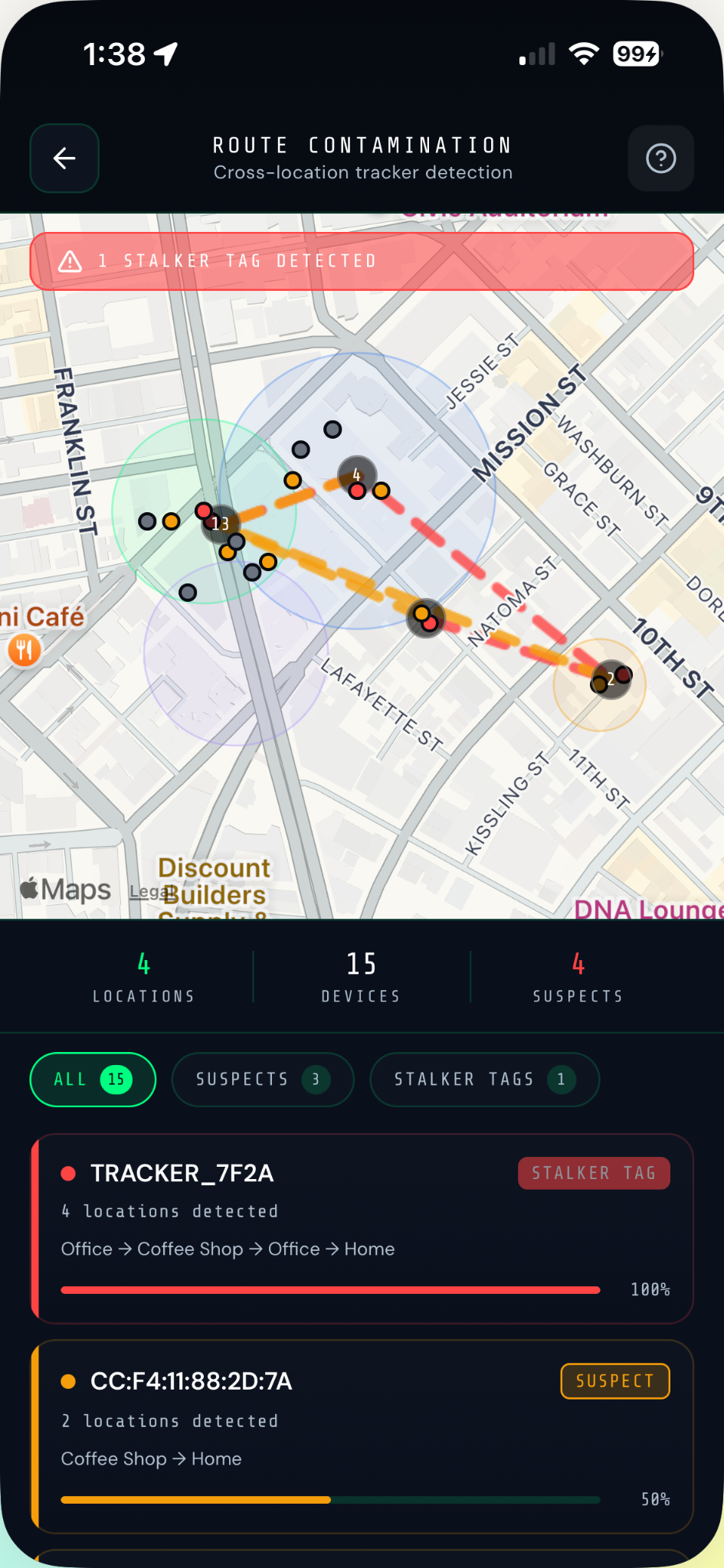
Builds a geographic timeline of every device seen across multiple scan sessions. When a device crosses a configurable distance threshold at 3+ separate locations alongside you, it triggers an immediate stalker alert.
Once a suspicious device is identified, the UWB Proximity Tracker displays real-time estimated distance and bearing — so you can physically locate a hidden tracker to within a few meters before it follows you anywhere else.
24-hour radial charts detect COMMUTE, WORKDAY, NIGHTTIME, and SPORADIC patterns. A Follow Score (0–100) across 5 dimensions flags followers. ESCALATING trend badges show if a threat is growing.
Generate a PDF with a unique case number (VW-YYYYMMDD-XXXX), full location timeline up to 50 entries, daily pattern clock, frequency trend, and a legal disclaimer — ready to share directly with law enforcement or an attorney.
High-contrast dark interface you can read fast — when it matters most.
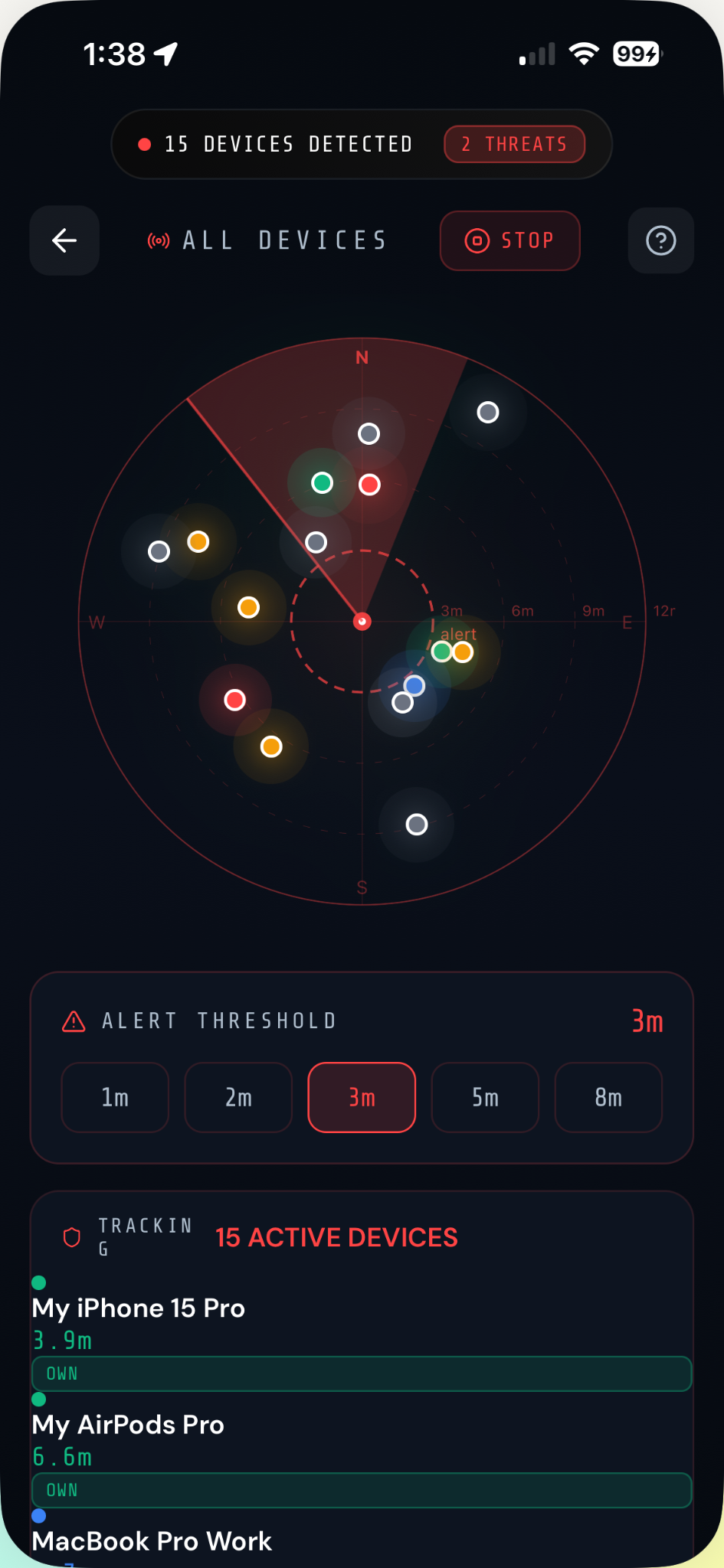


Tap once for an instant scan, run Continuous mode for a 30-second sweep, or set Interval mode (every 5–60 min) for all-day silent background monitoring. Every session is auto-archived.
Tag Fingerprinting identifies tracker brands from raw BLE ads. The Follow-Me algorithm calculates a Follow Score across 5 dimensions. Route Contamination maps movement history across sessions.
Use UWB Proximity Tracker to find a hidden device within meters. Export a PDF evidence report with a unique case number, full location timeline, pattern analysis, and legal disclaimer.
Most anti-stalking apps find only Apple's tags. VigilWatch is built for anyone — regardless of phone brand, tracker brand, or threat type.
Scans rogue access points, evil twin networks, and BLE trackers simultaneously in a single session.
PDF reports include unique case numbers, location timelines up to 50 entries, daily patterns, and a legal disclaimer — ready for law enforcement.
Locate a hidden tracker to within meters using the UWB Proximity Tracker — works for any BLE device, not just AirTags.
Identifies 7 tracker brands by raw BLE signature — including AirTag, Tile, Samsung SmartTag, Apple Find My Accessory, Google Find My Device, Chipolo, and TrackR.
Each platform brings a capability the other can't match. Both are built on the same core — the difference is in the hardware.
VigilWatch was designed from the ground up with privacy as a core principle — not an afterthought. There are no accounts, no servers, no tracking.
Most people don't know they're being tracked. VigilWatch changes that.
Join the waitlist and get early access to VigilWatch. Free to download. No subscription. No spam — just one email when we're live.
iOS & Android · SeaGlass Development
Connect with other VigilWatch users — share experiences, tips, and help each other stay safe. A support network for people who take their safety seriously.
Join Community →See how VigilWatch has been used to identify stalking trackers, suspicious devices at hotels, and unknown Bluetooth sniffers in coffee shops and subways.
Read Case Studies →